FBI and Experts Warn About the Rise of Toll Road Scams: How to Protect Yourself and Your Business

The FBI, cybersecurity experts, and state officials have recently raised alarms about a new wave of toll road-related scams sweeping across the United States. These deceptive attacks, commonly known as “smishing” (SMS phishing), have targeted consumers with fraudulent toll payment notifications. What started as a simple scam to steal personal information has now escalated, with severe consequences not only for individuals but also for businesses.
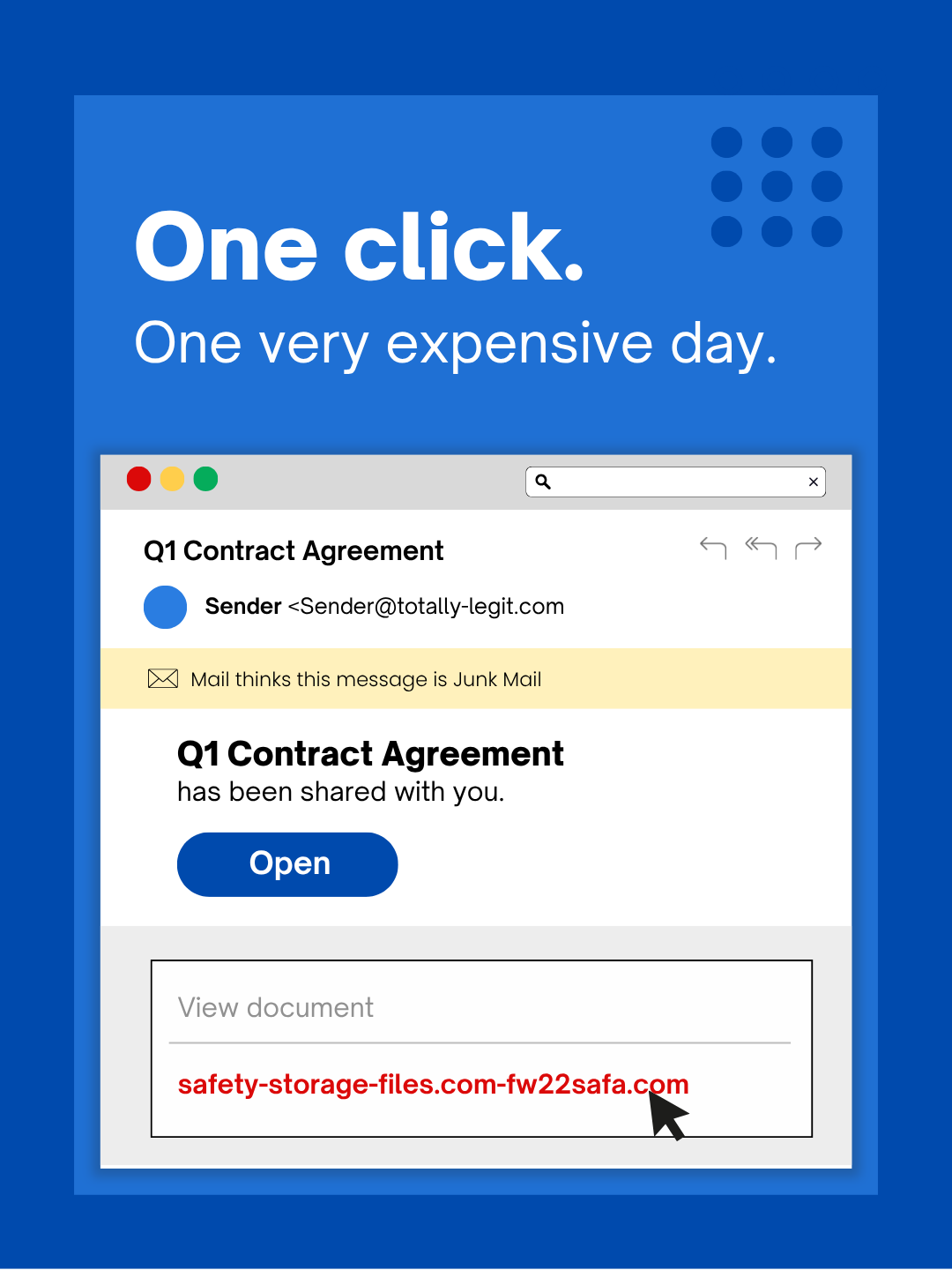
The typical toll road scam begins with an unsolicited text message claiming that the recipient has an unpaid toll or delivery charge requiring immediate payment. These messages usually contain a link that appears to direct the victim to a legitimate payment page. However, these links redirect users to fake websites designed to harvest sensitive personal data, including credit card numbers, bank account details, and even Social Security numbers.
Scammers often use a sense of urgency in their messages, claiming that failure to pay will result in higher fees or other severe consequences. These fake notifications sometimes extend beyond toll payments, incorporating fraudulent delivery services, making the scam appear even more legitimate. The aim is simple: to trick individuals into entering their sensitive data quickly, without taking the time to verify the authenticity of the request.
The scope of these scams has grown rapidly, with cybersecurity organizations such as Unit 42, McAfee, and the FTC reporting an alarming uptick in incidents across the country. Major U.S. cities, including Dallas, Atlanta, Los Angeles, Chicago, and Orlando, are among the hardest-hit regions. In some areas, local government officials, including Louisiana Attorney General Liz Murrill, have even personally been targeted, issuing public warnings to residents about the threat.
According to McAfee, these scams are not just limited to one area but are spreading to new regions at an alarming rate, with new reports surfacing each week from places like Detroit, Denver, and San Francisco. These scams are expected to continue their rapid growth as cybercriminals refine their techniques.
A major shift in the tactics of cybercriminals is the increasing focus on mobile devices. As Zimperium, a cybersecurity firm, warns, cybercriminals are moving to a “mobile-first attack strategy.” With smartphones becoming the primary device for many people to manage their personal and financial affairs, they are more likely to click on suspicious links in text messages than in emails.
This makes individuals particularly vulnerable to scams, as it’s much easier to fall for a scam in the smaller format of a text message, where it’s harder to spot red flags like suspicious web addresses or odd characters in the link. As the shift to mobile continues, the risks associated with smishing attacks are growing exponentially.
While these scams primarily target individuals, the consequences can be far-reaching:
- Financial Losses: Victims who enter payment information on fraudulent websites may find themselves with stolen money. Scammers can use the stolen data to make unauthorized charges or engage in further fraudulent activities.
- Identity Theft:
Beyond immediate financial harm, these scams can lead to long-term consequences, such as identity theft. Personal details like Social Security numbers, addresses, and dates of birth can be exploited to open fraudulent accounts, affecting victims' credit scores and financial security.
- Reputational Damage: For small business owners or self-employed individuals, falling for one of these scams could lead to reputational damage. Clients and partners may lose trust in those who have been compromised, leading to potential loss of business or opportunities.
While the immediate victims of these toll payment scams may be individuals, businesses are also at significant risk:
- Data Breaches: When a business owner or an employee falls victim to a scam, cybercriminals can gain access to sensitive company data. This includes customer information, financial details, and business banking credentials. A data breach can have far-reaching consequences, including legal action, regulatory fines, and loss of intellectual property.
- Financial Impact: Businesses that process payments through mobile devices or online platforms may be exposed to fraudulent charges if scammers gain access to payment details. The financial impact extends beyond immediate losses, as businesses may also incur additional costs in fraud detection and securing systems to prevent future breaches.
- Damage to Customer Trust: Trust is the foundation of any business, and it can be severely damaged if customers learn that a business has been tricked by scammers. Negative reviews, lost customers, and a tarnished reputation are just some of the fallout a company could face after such an incident.
- Legal Liabilities: Businesses are required by law to protect their customers’ and employees’ sensitive data. A breach due to a scam could expose a company to lawsuits, fines, and scrutiny from regulatory bodies. Data protection laws like GDPR (General Data Protection Regulation — a data privacy law enacted by the European Union) and CCPA (California Consumer Privacy Act — a data privacy law enacted by the state of California) make it clear that businesses are responsible for securing private information.
It’s essential to recognize the warning signs of a toll payment scam before falling victim:
- Suspicious URLs: Fraudulent links often contain misspelled or altered domains designed to look like legitimate toll websites. Be wary of links with extra hyphens or unusual characters (e.g., geauxpass-la.com instead of geauxpass.com).
- Urgency: Scammers use urgency as a tactic, pressuring victims to act immediately. Legitimate companies will never pressure you into paying an overdue charge through a text message.
- Unusual Payment Requests: If you are asked to enter payment details on an unfamiliar website or if you receive a pop-up indicating your card was declined, this is a red flag. Scammers may use these methods to capture payment information.
If you receive a suspicious toll payment text message, it’s essential to follow these steps:
- Do Not Click the Link: Never engage with unsolicited texts, especially those containing links or asking for payment information.
- Verify the Source: Always reach out to the toll agency directly using a known, legitimate phone number or website. Do not use the contact information provided in the text message.
- Report and Delete: Use your phone’s “report junk” feature to report the scam, or forward the message to 7726 (SPAM). Once reported, delete the message to avoid accidental clicks in the future.
- Secure Your Accounts: If you have entered any personal information or payment details, immediately take steps to secure your accounts. Change passwords, monitor bank statements, and report any suspicious activity.
Both the FBI and FTC offer clear advice for anyone who believes they’ve been scammed:
- File a Complaint: Report the scam to the Internet Crime Complaint Center (IC3) at www.ic3.gov. Include details such as the phone number the text originated from and the website provided in the message.
- Verify and Protect: Always check your accounts using legitimate websites, and contact customer service via known methods.
- Delete the Scam Text: Once you've verified and reported the scam, delete the message to avoid future risks.
As toll scams continue to evolve, it’s vital to stay vigilant and protect your personal and business data. These scams are no longer just a nuisance; they can result in significant financial and reputational damage. Whether you’re an individual trying to protect your finances or a business owner safeguarding company data, it’s crucial to verify any unsolicited messages and avoid clicking on suspicious links. By following the recommendations of cybersecurity experts and authorities, you can better protect yourself from falling victim to these increasingly sophisticated scams.
Doffman, Zak. "FBI Warning: Delete New Texts On Your Phone." Forbes, Forbes Media, 11 Mar. 2025, www.forbes.com/sites/zakdoffman/2025/03/11/fbi-warning-delete-new-texts-on-your-phone/.
Like this article? Share it!
The Best IT Support in Houston TX!
Check out our reviews to find out why!
Check out our TESTIMONIALS PAGE and you'll see we are the best choice for your IT Managed Services. We have the highest ratings in Houston Area for IT Services & Managed Services. Book a free consultation to find out how we can secure your business for you! IT Managed Services in Houston, Texas
READ MORE OF OUR ARTICLES!
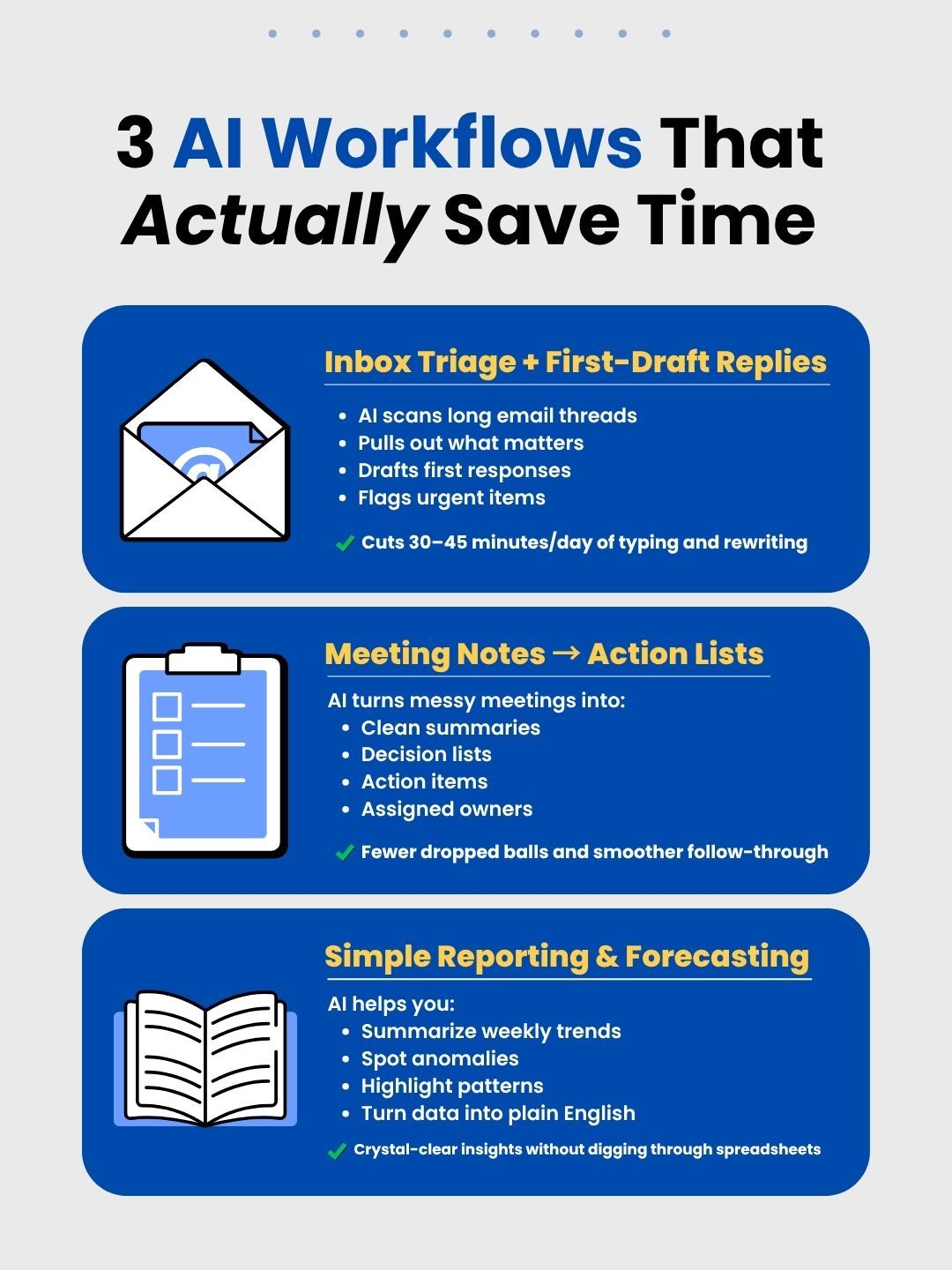
AI tools are everywhere right now. Every app you open is pushing some ver sion of “Add AI,” “Automate with AI,” or “Use AI or fall behind.” And most business owners are thinking the same thing: This sounds great! But where does this actually help and how do I make sure it doesn’t create more problems than it solves? That’s the right question. Because AI today is basically the new intern everyone hired without training. Interns can be incredibly helpful...but they can also send the wrong email, misinterpret instructions, or create more work if no one sets clear expectations. AI works the same way. Used well, it saves time and improves efficiency. Used poorly, it creates confusion, exposes sensitive data, and leads to costly mistakes. So let’s take a practical approach. 3 AI Uses That Actually Save Time in a Small Business Not every AI tool is worth your attention. But there are a few areas where it consistently delivers real value. 1) Inbox Management and First-Draft Responses If your inbox constantly feels overwhelming, AI can help you get it under control. It’s especially effective at scanning long email threads, identifying key points, and drafting a solid first response. It can also flag messages that need your attention so nothing slips through the cracks. Where it falls short is context and nuance. So the workflow is simple: AI drafts. Human approves. Many small businesses are already seeing results...cutting 30 to 45 minutes of email time each day without sacrificing quality. 2) Meeting Notes → Action Lists Meetings don’t just take time. They often create confusion afterward. AI note-taking tools can summarize conversations, pull out decisions, create action items, and assign owners. Instead of wondering what was decided or who is responsible, your team leaves with clarity. The result is fewer dropped tasks, faster follow-through, and less time spent rewriting notes no one reads. 3) Simple Reporting and Forecasting Most businesses aren’t short on data. They’re short on time to interpret it. AI can summarize trends, highlight anomalies, surface patterns, and turn raw numbers into plain English. Not as a crystal ball—but as a tool that helps you make faster, clearer decisions. The Guardrails: How to Use AI Without Creating Risk This is where most businesses run into trouble. AI feels easy to use, so teams start treating it like a search engine—and that’s when sensitive information gets shared without thinking. Here are the rules: Rule #1: Never paste sensitive data into public AI tools Customer data, payroll information, financial records, passwords, or anything confidential should never be entered into public AI tools. If you wouldn’t want it exposed, don’t paste it. Rule #2: Control who can use what “Shadow AI” is growing quickly. Employees sign up for tools on their own to be efficient—good intent, risky outcome. You need a short approved tools list and clear guidelines on what can and cannot be used. Rule #3: AI drafts, humans decide AI is great at first drafts. but it can also be confidently wrong. Anything that goes out to a client or represents your business should always be reviewed and approved by a human. Rule #4: Assume everything you type is stored Many AI tools store or process what you enter. Treat everything you type as if it could live outside your organization. Rule #5: When in doubt, don’t paste If someone isn’t sure whether something is appropriate to share, the safest move is to stop and ask. Five simple rules: strong enough to prevent most AI-related mistakes. What This Looks Like in a Real Business AI done right isn’t complicated. A business: • Picks 1–2 processes where time is being wasted • Adds AI with clear rules • Measures the impact • Expands slowly Not a massive transformation. Just practical improvements. The businesses pulling ahead aren’t the ones using the most AI. They’re the ones using it intentionally. Where an MSP Can Help This is where many business owners start to feel overwhelmed. You don’t want to: • Test dozens of AI tools • Guess what’s secure • Write policies from scratch • Wonder if your data is being exposed A good MSP helps by: • Recommending the right tools • Locking down access and permissions • Creating simple, usable policies • Monitoring for risky behavior • Integrating AI into your workflow without adding complexity The goal is simple: make AI useful without introducing new risks. Where Does Your Business Stand? If your team is already using AI with clear guidelines in place, you’re ahead of most businesses. If you’re unsure how AI is being used, or what might be getting shared, it’s worth addressing now. Because the question isn’t whether your team is using AI. It’s whether they’re using it safely. Want help setting up AI guardrails that actually work? 👉 Book a quick 10-minute call and we’ll walk through your setup, identify risks, and help you put simple protections in place.

You’re halfway to the beach. The kids are asking for snacks. Someone spilled something in the back seat. Your phone is buzzing with work notifications. Then your child asks: “Can I use your laptop to watch YouTube?” or "...to pla Roblox?" Your work laptop. The one with client files, financial data, and access to your entire business. You’re tired. The drive is long. The beach is still two hours away. What’s the harm? Actually… a lot. Spring break travel is the perfect storm for cybersecurity mistakes. You’re distracted, using unfamiliar networks, and mixing work and vacation in ways you normally wouldn’t. The good news: with a few simple habits, you can protect your business without ruining anyone’s vacation. Before You Leave: The 15-Minute Prep Before you pack the sunscreen and swimsuits, spend 15 minutes locking down your devices. Device basics • Install any pending security updates • Back up important files to the cloud • Turn on automatic screen locking (2 minutes max) • Enable “Find My Device” on phones and laptops • Charge your portable battery pack • Pack your own charging cables and adapters Public charging stations exist… but they aren’t always safe. The family conversation Before the trip starts, set expectations. • Explain which devices are off-limits for kids • Set up a family tablet or travel device for entertainment • If kids must use your laptop, create a separate user account Pro tip: A $150 tablet is a lot cheaper than a data breach. Hotel WiFi: Everyone Uses It Wrong You finally arrive. Within five minutes everyone is connected to the hotel WiFi. Phones. Tablets. Laptops. Game consoles. Your teenager is streaming Netflix. Your spouse is checking email. You’re trying to send one quick proposal before dinner. Here’s the problem: Hotel WiFi networks are shared by hundreds of guests. And sometimes… by hackers too. A common scam is a fake WiFi network that looks like the hotel’s. Guests connect to it and unknowingly send passwords, credit card numbers, and emails straight to an attacker. How to stay safe Verify the network name Ask the front desk for the exact WiFi name. Don’t guess. Use a VPN for work access This encrypts your connection. Use your phone hotspot for sensitive work Banking, client files, or confidential documents should never go through hotel WiFi. Separate work from entertainment Kids streaming cartoons on hotel WiFi? Fine. Accessing business systems? Use your hotspot. The “Can I Use Your Laptop?” Problem Your work laptop contains: • Email • Client files • Banking information • Business systems Your kids just want to: • Watch YouTube • Play games • Video chat friends Kids don’t mean to cause problems, but they: • Click pop-ups • Download things • Save passwords • Forget to log out On a work device, that’s a security risk. The safest rule Just say: “This is my work computer. You can use the tablet instead.” Consistency matters. If you absolutely must share • Create a separate restricted user account • Supervise what they’re doing • Don’t allow downloads • Don’t save passwords • Clear browsing history afterward Best plan Bring a dedicated family device for travel. Streaming on Hotel TVs: The Log-Out Trap You sign into Netflix on the hotel TV. The kids watch a movie. The next morning you leave for the beach… and forget to log out. Now the next guest has access to your account. And if you reuse passwords (hopefully you don’t), they might try it elsewhere. Easy fixes • Cast from your phone or tablet instead • Set a reminder to log out before checkout • Download shows before traveling and skip the hotel TV entirely Never log into these on hotel TVs: • Banking apps • Work accounts • Email • Social media • Any account with payment info saved What To Do If A Device Goes Missing Travel is chaoti Devices get left in restaurants, hotel rooms, airport security bins, and rental cars. If something goes missing: Within the first hour 1. Use Find My Device to locate it 2. Lock the device remotely 3. Change passwords for critical accounts 4. Contact your IT provider or MSP 5. Notify anyone affected if sensitive data was on the device Before you travel, make sure devices have: • Remote tracking enabled • Strong password protection • Automatic encryption • Remote wipe capability The Rental Car Data Trap You connect your phone to the rental car to play music or use navigation. Many cars store: • Contacts • Call logs • Message previews When you return the car… that data often stays there. The 30-second fix before returning the car • Delete your phone from the car’s Bluetooth settings • Clear recent destinations from the GPS • Or skip pairing entirely and use an AUX cable The “Working Vacation” Problem You promised yourself this trip would be different. But somehow you’ve: • Checked email 47 times • Taken three “quick” work calls • Spent an hour on your laptop while everyone else played mini-golf Besides frustrating your family, constantly switching between work and vacation lowers your security awareness. You’re distracted and more likely to click something you shouldn’t. If you can’t fully unplug Set clear boundaries: • Check work email twice per day only • Use your phone hotspot for work tasks • Work in your hotel room, not public areas • Be fully present when you’re with family The best cybersecurity practice? Actually taking a break. The Spring Break Security Mindset Travel is messy. The goal is to be intentional about risk. Remember to: • Prepare devices before you leave • Know which activities are risky • Separate work and family devices when possible • Have a plan if something goes wrong • Be comfortable saying: “Not on this device.” Make Spring Break Memorable For The Right Reasons Spring break should be about beach sunsets, road trip playlists, and late-night ice cream runs. Not explaining to clients why their data was compromised. A few simple habits can protect your business without ruining the trip. Your family gets the vacation. Your business stays secure. Everyone wins. 👉 Schedule your free security consultation Because the worst spring break memory shouldn’t be: “Remember when Dad’s laptop got hacked at the beach?”
January is a powerful month. For a few weeks, everything feels fresh. Goals are written down. Budgets are approved. Big plans are set in motion. Then February arrives. Client requests pile up. A printer jams. Someone can’t access a file they need immediately. And the resolution to “finally get our IT under control this year” quietly slides to the bottom of the priority list. Sound familiar? The Real Reason Business Tech Resolutions Fail Most business technology goals don’t fail because of laziness or lack of discipline. They fail because they depend on willpower. And willpower is unreliable once the year gets busy. By February, urgency replaces enthusiasm. The problem isn’t motivation. It’s structure. Why This Mirrors Gym Memberships Every January, gyms are packed. By mid-February, attendance drops dramatically. It’s not because people stopped caring about their health. It’s usually because the goal was vague, there was no accountability, no clear plan, and no expert guidance. Business technology works the same way. “We need better backups.” “Our security could be stronger.” “We should upgrade these computers.” These aren’t bad intentions. They’re just unsupported ones. Structure Beats Willpower Every Time People who consistently reach fitness goals often work with trainers. Not because they are more disciplined, but because they have a system. A trainer provides: • A clear plan • Accountability • Consistency • Proactive adjustments That’s exactly what a strong managed IT partner provides for a business. The MSP as Your Business’s Personal Trainer When you work with a managed IT provider, you’re not just outsourcing support tickets. You’re installing structure. Backups are tested, not assumed. Hardware is replaced on a schedule, not when it fails. Security is monitored continuously. Small issues are addressed before they become emergencies. Instead of reacting to fires, you prevent them. What This Looks Like 90 Days Later Imagine a 25-person firm where nothing is technically broken — but everything feels slow and slightly frustrating. Random outages. Aging equipment. Lingering security concerns. Within 90 days of implementing a structured IT plan: • Backups are verified • Replacement schedules are mapped out • Security gaps are closed • Productivity improves Nothing flashy. Just stability. And stability allows growth. The Only Resolution That Matters in February If you make one business technology decision this year, make it this: Stop operating in firefighting mode. Not “digital transformation.” Not “modernizing infrastructure.” Simply remove daily friction. Because when technology is predictable: • Your team works faster • Clients receive better service • Billable hours increase • Growth feels manageable Reliable technology is scalable technology. And scalable technology creates freedom. Make February Different January motivation fades. That’s normal. Instead of relying on enthusiasm, make one structural decision that continues working even when you’re busy. Book a Tech Reality Check. 30 minutes. No jargon. No pressure. Just clarity. Because the best resolution isn’t “fix everything.” It’s “stop doing it alone.”
Every January, tech headlines explode with bold predictions about the “next big thing” that will supposedly transform business overnight. By the time February rolls around, many small business owners are left overwhelmed by jargon — AI this, blockchain that, metaverse something — without a clear sense of what will truly move the needle for a company with 10–25 employees trying to grow sustainably. Here’s the reality: most technology trends are marketed hype designed to sell high-priced consulting services. But underneath the noise, a handful of real shifts are quietly reshaping how small businesses will operate in 2026. Let’s strip away the buzzwords. Below are three technology trends worth paying attention to — and two you can confidently ignore. Tech Trends Worth Your Attention in 2026 1. AI Embedded Directly Into the Tools You Already Use What this really means: In recent years, AI felt like a separate skill you had to learn. You opened a tool like ChatGPT, typed a prompt, copied the result, and pasted it somewhere else. In 2026, that separation is disappearing. Artificial intelligence is now being built directly into everyday business software — the platforms your team already logs into daily. Your email platform drafts replies. Your CRM suggests follow-up messages. Your project management software turns meeting notes into task lists. Your accounting system auto-categorizes expenses and highlights unusual activity. Real-world examples: Microsoft Copilot is integrated into Word, Excel, PowerPoint, and Outlook. Google Workspace offers AI features across Docs, Sheets, and Gmail. QuickBooks uses AI to categorize transactions and surface potential deductions. Slack can summarize long message threads in seconds. Why it matters: You are not adopting brand-new tools — you are upgrading the ones you already use. That dramatically lowers the learning curve. Instead of asking, “Should we use AI?” the better question becomes, “Are we turning on the features we’re already paying for?” What to do: When your software platform introduces AI features in 2026, don’t dismiss them immediately. Test them in real workflows for a couple of weeks. Some will feel unnecessary. Others will quietly save hours every month. Time investment: Minimal. You’re already using the software. 2. Automation That No Longer Requires a Technical Expert What this really means: For years, automation sounded appealing but impractical. Building workflows usually meant hiring a developer or spending hours learning complicated tools. That barrier is rapidly disappearing. In 2026, many automation platforms allow you to simply describe what you want in plain language — and the system builds it for you. Instead of configuring complex rules, you can say: “When someone submits our contact form, add them to our spreadsheet, send a welcome email, and remind me to follow up in three days.” The automation handles the rest. Real-world example: A small law firm wanted new inquiries to automatically create case files, schedule consultations, and send intake forms. Previously, this required custom development or deep Zapier knowledge. In 2026, they explained the workflow, reviewed the setup, tested it, and launched — all in under an hour. Why it matters: Automation is shifting from “We should do this someday” to “We can set this up today.” Tasks that once stalled due to complexity are now accessible to non-technical teams. What to do: Pick one repetitive weekly task your team handles manually. Use an automation tool to describe the process and see what it generates. Start small and low-risk. Time investment: About 20–30 minutes to set up, then it runs continuously. 3. Cybersecurity Is Becoming a Legal Requirement, Not a Recommendation What this really means: For a long time, cybersecurity for small businesses was considered optional — smart to have, but rarely enforced. That is no longer the case. Privacy laws are expanding. Industry regulations are tightening. Insurance companies are requiring specific safeguards. Most importantly, enforcement is becoming real. In 2026, “We were hacked but didn’t have basic protections in place” increasingly leads to fines, denied insurance claims, lawsuits, and personal liability — not sympathy. Real-world examples: Public companies are now required to disclose material cybersecurity incidents within days. State attorneys general are penalizing businesses for weak data protection. Cyber insurance providers are rejecting claims when multifactor authentication isn’t enabled. Why it matters: Security is moving from a best practice to a baseline obligation. Skipping fundamentals is becoming as risky as operating without business insurance. What to do: At a minimum, ensure these three basics are in place: • Multifactor authentication on all business accounts • Regular data backups — and tested restores • Written cybersecurity policies that your team actually follows These steps are not complicated or expensive, but they are increasingly expected. Time investment: 2–3 hours to set up correctly, then minimal ongoing effort. Tech Trends You Can Safely Ignore 1. The Metaverse and Virtual Reality for Most Businesses Why it’s not worth your time: Virtual business environments have been hyped for over a decade — from Second Life to Meta’s rebrand. Yet for most small businesses, the problems VR claims to solve already have simpler answers. VR headsets remain costly, uncomfortable for extended use, and unnecessary for routine collaboration. A video call is still faster, cheaper, and easier. When it does make sense: Industries like architecture, real estate, and specialized design may benefit from 3D visualization. For most others, it adds complexity without clear returns. What to do: Nothing. If VR becomes essential, you’ll see competitors using it successfully. Until then, skip it. 2. Accepting Cryptocurrency Payments Why it’s usually a bad fit: Every few years, businesses ask whether they should accept crypto payments to appear cutting-edge. In practice, it often introduces more friction than benefit. Crypto is volatile, creates accounting headaches, adds tax complexity, and usually comes with higher processing fees. Meanwhile, the number of customers who genuinely want to pay with crypto remains very small. When it might make sense: If you operate internationally or have a customer base actively requesting crypto, it may be worth exploring. What to do: Politely decline and offer standard payment options like cards, checks, or ACH transfers. If real customer demand emerges, you can revisit later. The Bottom Line The most valuable technology isn’t the trendiest — it’s the technology that solves problems you already have. In 2026, small businesses should focus on: • AI features built into existing tools • Simple, accessible automation • Meeting baseline cybersecurity requirements You can safely ignore metaverse hype and crypto pressure unless your specific industry demands otherwise. Need help figuring out which 2026 tech trends actually apply to your business? Schedule a free consultation with our team. We’ll review your current setup and give practical recommendations that make operations easier — not more complicated. 👉 Schedule your free consultation by clicking here! Because the best tech decision is the one that saves time, reduces stress, and helps your business run better.

Every year, business owners are promised the next big thing in technology. New apps. New tools. New systems that claim to “change everything.” Most don’t. But in 2025? A handful of simple, practical tech changes actually made running a small business easier, safer, and less stressful. Not flashy. Just effective. Here are the real tech wins that helped small business owners save time, protect their data, and reduce daily headaches—without adding complexity. 1. Automatic Invoice Reminders That Actually Got Businesses Paid Faster Chasing invoices is one of the biggest time drains for small business owners. In 2025, many finally turned that task over to automation—and the results were immediate. Accounting tools like QuickBooks, FreshBooks, and Xero made it easy to set up automatic payment reminders. Once configured, invoices went out on schedule, reminders followed automatically, and awkward follow-up emails disappeared. Why it worked: • Clients received consistent, professional reminders • Payments arrived faster • Business owners reclaimed hours of admin time Instead of manually tracking who owed what, owners could focus on serving clients and growing revenue. 2. AI Tools That Actually Saved Time (Instead of Creating More Work) AI finally moved beyond hype and into helpful territory. Rather than replacing people, tools like ChatGPT, Microsoft Copilot, and Grammarly quietly took over repetitive tasks—drafting emails, summarizing meetings, organizing notes, and generating first drafts of documents. The result? • Less time spent staring at blank screens • Faster turnaround on routine work • More mental energy for decision-making and strategy The biggest win wasn’t automation—it was clarity. AI handled the busywork so business owners could focus on the work that actually matters. 3. Simple Security Upgrades That Prevented Major Headaches Cybersecurity doesn’t need to be complicated to be effective. In 2025, a few basic changes proved to go a long way. Businesses that implemented these saw the biggest improvements: • Multi-factor authentication (MFA) on email and business accounts • Password managers instead of reused passwords • Automatic device locking and encryption These small steps blocked the vast majority of common cyberattacks. No expensive software. No complicated setup. Just smart basics done consistently. 4. Cloud Tools That Made Work Truly Mobile The idea of “working from anywhere” finally became practical—not chaotic. Cloud platforms like Google Workspace, Microsoft 365, and Dropbox allowed teams to: • Access files securely from any device • Share documents without emailing attachments • Collaborate in real time Business owners could review proposals from their phone, approve documents on the go, and keep projects moving without being tied to a desk. Work became more flexible without sacrificing security. 5. Communication Tools That Cut Through the Noise Email overload has been a problem for years. In 2025, more teams moved conversations to tools like Slack and Microsoft Teams—and it made a noticeable difference. Instead of overflowing inboxes: • Messages became easier to track • Conversations stayed organized by topic • Teams responded faster without constant email chains The result? Clearer communication, fewer missed messages, and less time spent searching for information. The Bigger Picture: Simplicity Wins The biggest lesson from 2025 wasn’t about flashy tech or complex systems. It was this: The best technology quietly makes your workday easier. The tools that succeeded weren’t the most advanced—they were the ones that removed friction, saved time, and supported real workflows. Planning for the Year Ahead As you look ahead, ask yourself: • Which tools genuinely make my business run smoother? • What systems create stress instead of solving problems? • Where could a simple upgrade save time every single week? You don’t need more technology—you need the right technology. Want Help Simplifying Your Tech Stack? At Quinn Technology Solutions, we help small businesses streamline their technology, improve security, and eliminate unnecessary complexity. We focus on practical, real-world solutions—not buzzwords. 👉 Schedule your free discovery call today Let’s make your tech work for you, not against you.